AGTP: The Protocol the Agent Economy Has Been Missing
The web runs on HTTP. It will continue to run on HTTP. And AI agents will continue to limp along on it too, until the cost of that architectural mismatch becomes too expensive to ignore.
That cost is already accumulating. It shows up in agent identity systems that each vendor builds independently, in credential models that are fundamentally incompatible across platforms, in governance frameworks that cannot read each other’s trust signals, and in the CIO’s inbox as dozens of vendors each holding, in the words of GitLab’s CIO in a recent ZDNET feature, the keys to the kingdom.
Written by Joe McKendrick, the article highlights several problems with the shift to agent management, including cost, trust, and identity. These are challenges on HTTP.
What HTTP Was Designed For
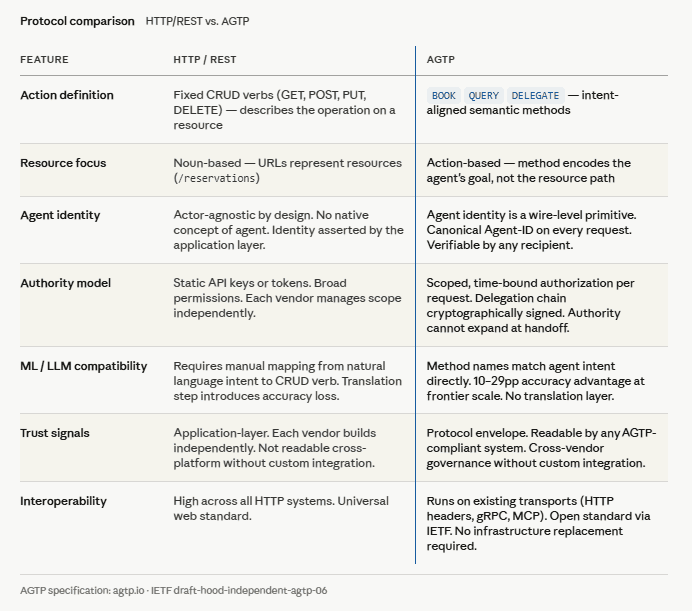
HTTP was designed for browsers fetching documents. GET this page. POST this form. The verbs describe operations on resources. The architecture assumes a human somewhere in the chain, initiating the request, interpreting the response, and deciding what to do next.
Every problem the agent management conversation now centers on is downstream of one architectural fact: agents are using a protocol that was never designed to recognize them.
HTTP is actor-agnostic by design. It cannot tell whether its caller is a human, a script, or an AI agent operating within a governance framework and under a behavioral contract. That agnosticism was a feature of HTTP’s original purpose. For agent traffic, it is the source of most of the hard problems.
Agent identity has to be asserted by the application, not verified by the protocol. Trust signals have to be managed by the management platform the organization installed, not read at the wire level by any system that receives the request. Credential scope has to be negotiated by each vendor independently, which is why agents accumulate static keys with broad permissions that nobody explicitly intended to grant.
The fragmentation is happening in the protocol. The management platform market is compensating for it. But compensation is not the same as resolution.
What AGTP Adds
The Agent Transfer Protocol is designed specifically for agent-to-system and agent-to-agent traffic. It runs on existing transports — HTTP headers, gRPC metadata, MCP session context, message queue headers — so adopting it does not require replacing infrastructure. What it adds is the agent-aware envelope that HTTP cannot provide.
Four primitives. Each addresses a problem that the current infrastructure solves expensively, inconsistently, or not at all.
Native agent identity. Every agent on AGTP carries a cryptographic identity issued at registration and verifiable by any participant in a transaction. This is not a management platform feature that requires a specific vendor’s tooling to read. It is a protocol-level fact present in every request and readable by any system that speaks the protocol. Shadow agents produce traffic that lacks the identity envelope. The absence is detectable. Discovery stops being a function of which management tool was installed and becomes a property of the protocol itself.
Verifiable trust. Trust signals travel in the protocol envelope. A receiving system can evaluate a request based on protocol-level evidence about the agent’s authority, behavioral history, and drift state, without querying a specific vendor’s database in real time. Cross-vendor governance becomes tractable because the trust evidence is in the request, not in a proprietary registry. An orchestrator on one platform can delegate to an agent on another, with the delegation chain cryptographically verifiable by the receiving system without assuming any shared vendor relationship.
Authority chains and scoped credentials. Agents operating on AGTP do not hold static credentials with broad permissions. They request scoped, time-bound authorization at the moment of need. Every delegation step is cryptographically signed. Authority cannot expand at handoff; a subagent can only operate within the scope explicitly delegated to it for the specific task. The CIO problem dissolves because no agent ever holds static broad access. The keys are scoped, bounded, and auditable by design.
Embedded budgetary metering. Cost and authority limits travel with the request. An agent that exceeds its budget is throttled at the protocol layer before downstream systems respond. This matters now for cost control and will matter more as the industry’s billing models evolve. Whether the unit of account is tokens, compute, or governed actions, the metering primitive remains stable because it operates on the authorization layer rather than on any particular billing abstraction.
The Problems This Solves
The practitioner conversation about agent management has produced a consistent list of pain points. Agent sprawl with no reliable inventory. Credential proliferation with no systematic governance. Shadow agents operating outside visibility. Duplicated tooling is built by every vendor to solve the same foundational problem. Lock-in fears when governance infrastructure becomes inseparable from a specific vendor’s platform. Cost unpredictability occurs as agents accumulate access and consume resources without bounded authorization. Cross-vendor governance that requires each platform to communicate with every other platform via custom integrations.
Every item on that list is a protocol-level problem being addressed at the platform level. When the protocol knows what an agent is, when identity, authority, trust, and metering are protocol-layer primitives rather than application-layer assertions, the platform-level compensation becomes unnecessary.
Agent sprawl is addressed because every agent is identifiable by protocol definition, not by tool installation. Credential proliferation is addressed because, by design, scoped brokered authorization replaces static keys. Shadow agents are visible because traffic without protocol identity is structurally distinguishable. Duplicated functionality collapses when the identity layer is standardized across platforms. Lock-in fears reduce because an open protocol can be spoken by any compliant implementation. Cost unpredictability becomes manageable because the budget travels with authorization rather than being tracked separately. Cross-vendor governance becomes possible because trust signals are readable across organizational boundaries at the wire level.
An Open Standard, Not a Vendor Feature
AGTP is being developed as an open standard. The specification is published at agtp.io. The IETF individual submission is available at the datatracker. The GitHub repository is open. Reference implementations are being built.
Nomotic is the first agent management platform implementing AGTP natively. The protocol is deliberately not Nomotic’s property. Standards do not become standards because one vendor owns them. The architectural commitment is that agent infrastructure built on AGTP is portable, interoperable, and not dependent on any single vendor’s continued participation.
The question for organizations beginning to think seriously about how their agent infrastructure will look as deployments scale is direct. Do you want that infrastructure built on a protocol designed for document retrieval, with identity and governance retrofitted at the application layer by each vendor independently? Or on a protocol designed from the beginning for agents, where identity, authority, trust, and metering are wire-level facts?
The web ran on HTTP because HTTP solved the right problem at the right layer. The agent economy needs its own answer to that question. AGTP is the attempt to write it at the right layer before the retrofitting debt becomes the infrastructure.
If you find this content valuable, please share it with your network.
Follow me for daily insights.
Book me to speak at your next event.
Start managing your agents for free.
Chris Hood is an AI strategist and author of the #1 Amazon Best Seller Infailible and Customer Transformation, and has been recognized as one of the Top 30 Global Gurus for Customer Experience. His latest book, Unmapping Customer Journeys, is available now!